Product docs and API reference are now on Akamai TechDocs.
Search product docs.
Search for “” in product docs.
Search API reference.
Search for “” in API reference.
Search Results
results matching
results
No Results
Filters
Monitoring and Securing Cloud Workloads With Wazuh
Traducciones al EspañolEstamos traduciendo nuestros guías y tutoriales al Español. Es posible que usted esté viendo una traducción generada automáticamente. Estamos trabajando con traductores profesionales para verificar las traducciones de nuestro sitio web. Este proyecto es un trabajo en curso.
Wazuh is an open-source security platform that offers unified extended detection and response (XDR) and security information and event management (SIEM) protection for endpoints and cloud workloads.
Wazuh is an efficient way to secure your cloud computing processes, containers, and Kubernetes pods, as well as your client computers and devices. Wazuh can also help you meet government requirements such as PCI DSS, HIPAA, and GDPR, as well as configuration standards such as CIS hardening guides.
How Does Wazuh Work?
Wazuh performs log data analysis, intrusion and malware detection, file integrity monitoring, configuration assessment, vulnerability detection, and supports regulatory compliance.
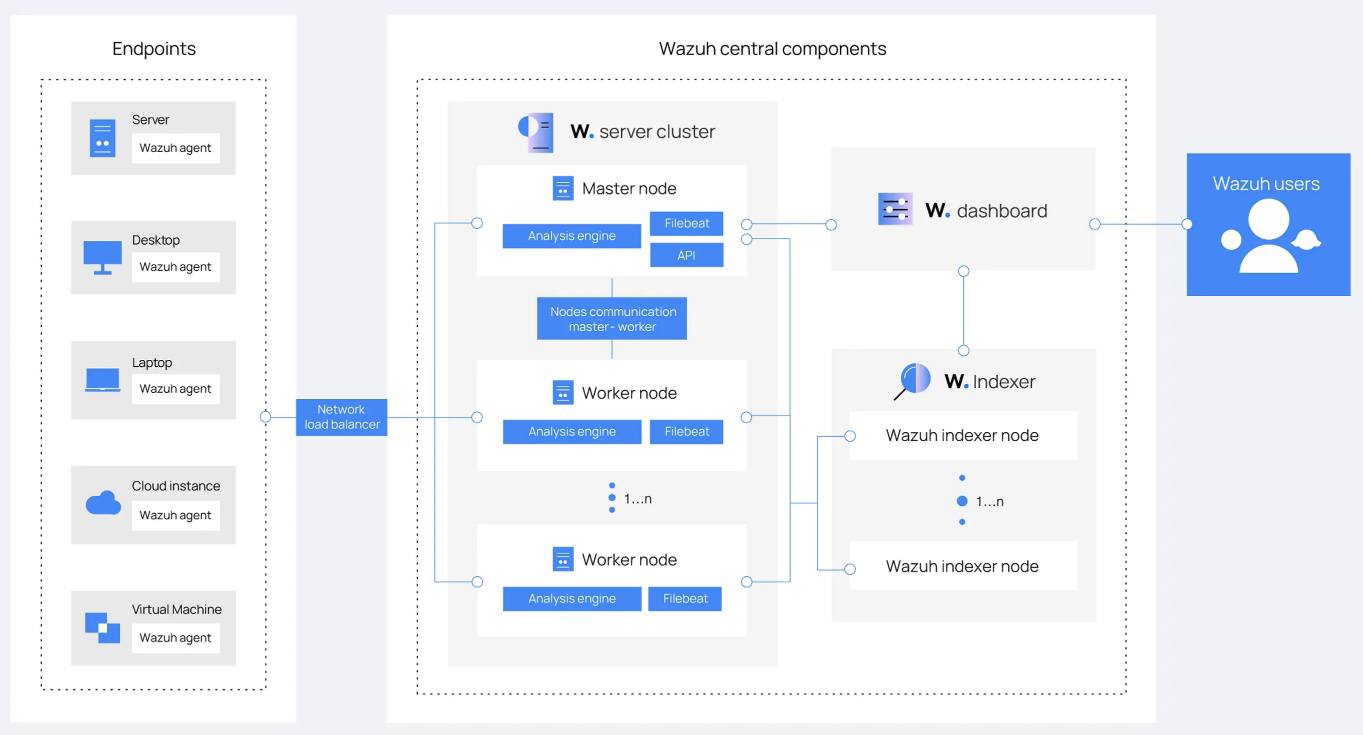
As displayed below, The Wazuh platform consists of: agents that monitor endpoints, servers that analyze the logs emitted by agents, indexers, and a dashboard. Wazuh users primarily interact with the dashboard.

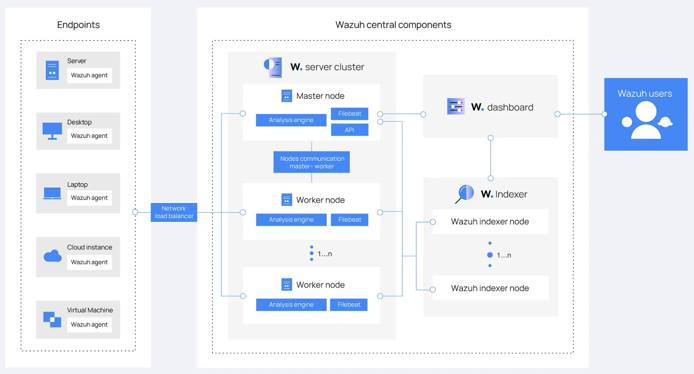
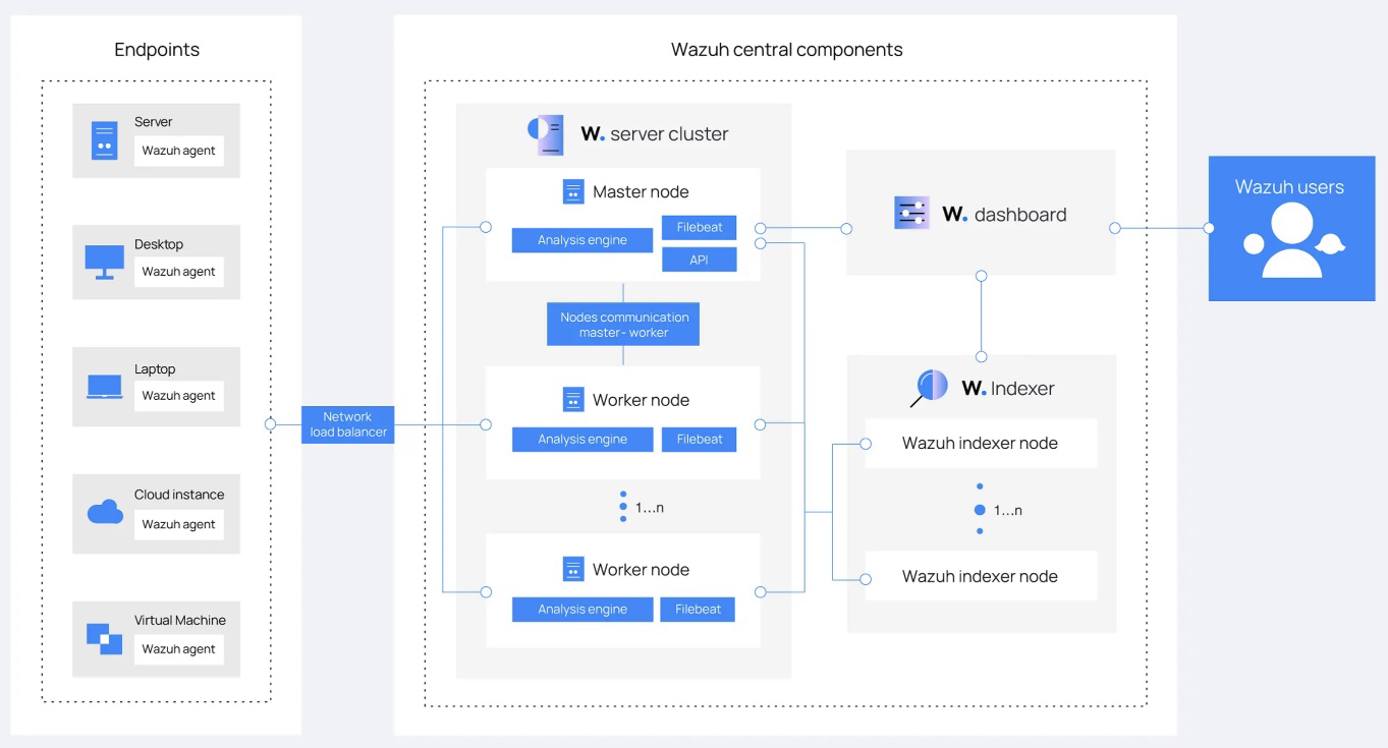
Wazuh Components
The Wazuh Indexer
The Wazuh indexer is a scalable full-text search and analytics engine. It indexes and stores alerts that the Wazuh server generates, and provides near real-time data search and analytics capabilities. You can configure the Wazuh indexer as a single-node or multi-node cluster. It stores data as JSON documents, and its database is sharded.
Wazuh uses four different indices to store different event types: alerts, archives, monitoring, and statistics. You can interact with the Wazuh indexer cluster using the Wazuh indexer REST API.
The Wazuh Server
The Wazuh server is a central component that analyzes the data received from the agents, triggering alerts when threats or anomalies are detected. You can also use it to manage and monitor agent configurations remotely.
The Wazuh server uses threat intelligence sources to improve its detection capabilities. It also enriches alert data by using the MITRE ATT&CK framework and regulatory compliance requirements such as PCI DSS, GDPR, HIPAA, CIS, and NIST 800-53, providing helpful context for security analytics. Additionally, the Wazuh server can be integrated with external software, including ticketing systems and instant messaging platforms.
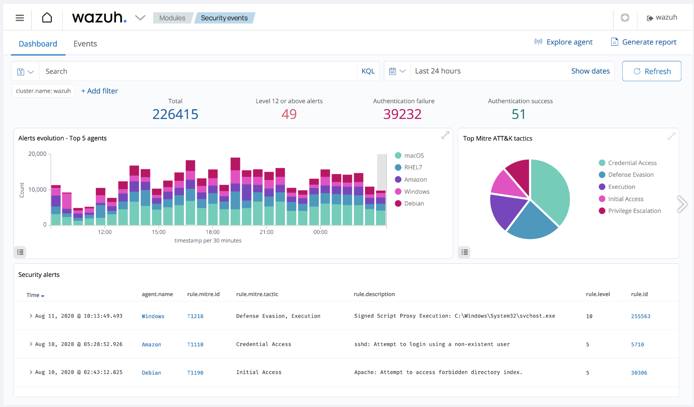
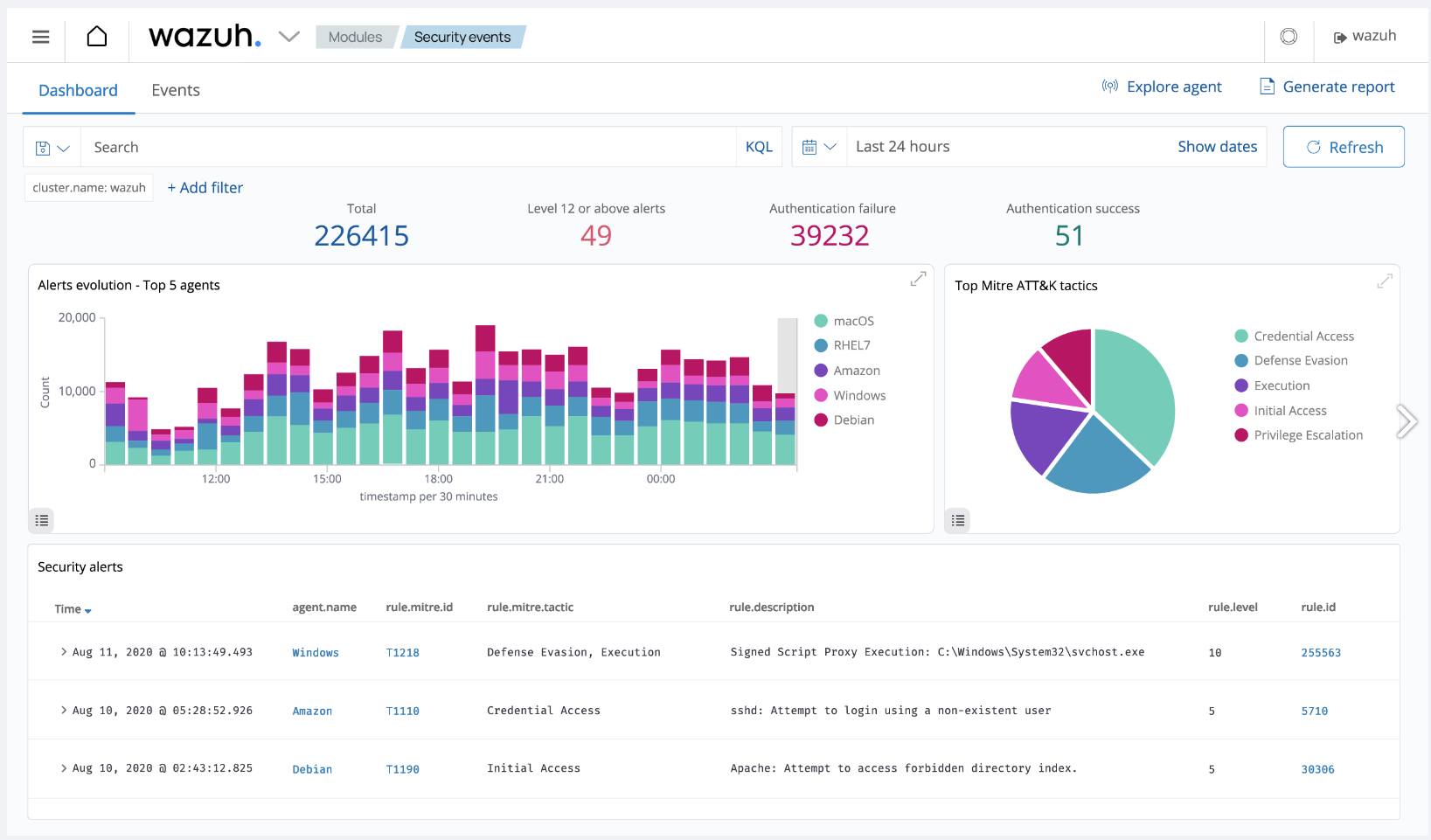
The Wazuh Dashboard
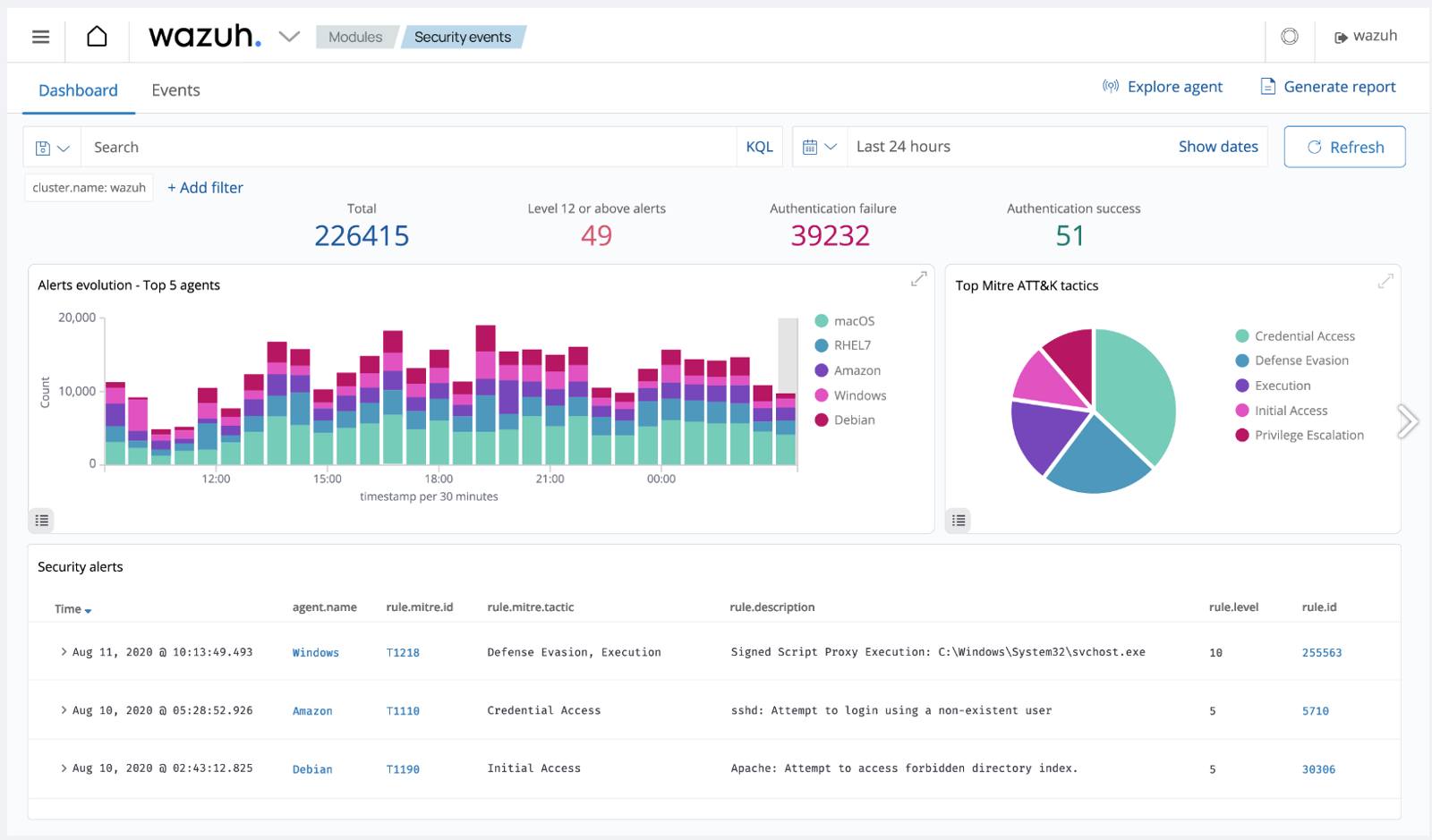
The Wazuh dashboard provides a web-based interface designed for mining, analyzing, and visualizing data related to: security events, alert data, platform management, and platform monitoring. It encompasses functionalities for role-based access control (RBAC) and single sign-on (SSO).
Wazuh features dashboards for exploring the MITRE ATT&CK framework and associated alerts, fostering enhanced situational awareness and threat analysis.

How to Install and Configure Wazuh
There are a number of ways to install Wazuh, depending on where you want it to run, what other services you want to use with Wazuh, and the amount of traffic you need to handle:
Use our Wazuh Quick Deploy App for a fast deployment. This option fully deploys in about 15 minutes and requires minimal configuration information.
Using Wazuh’s Quickstart instructions along with their installation assistant, you can create an all-in-one, single node deployment. This deploys Wazuh on a single server that can monitor up to 100 endpoints.
Below are the Akamai plan types and minimum hardware recommendations for handling various numbers of monitoring agents:
Agents Akamai Plan Type 1–25 Shared, Dedicated, or Premium 8 GB with 4 CPUs 25–100 Shared, Dedicated, or Premium 16 GB with 6-8 CPUs For a customizable deployment, you can deploy Wazuh manually across multiple nodes (see Multi-Node Wazuh Installation below).
For development environments, you can deploy via Docker images.
For a scalable deployment, you have the option of installing Wazuh on Kubernetes.
Multi-Node Wazuh Installation
For a flexible installation of Wazuh, you can install both the Wazuh indexer and Wazuh server components manually on a single node or across multiple nodes for a cluster deployment. The Wazuh dashboard can be installed on one of your nodes running the Wazuh indexer or on a separate node.
During manual installation, components should be installed in the following order on one or more nodes:
- The Wazuh indexer
- The Wazuh server
- The Wazuh dashboard
Once all the components are installed, you can install individual Wazuh agents on the servers, computers, or other devices you wish to monitor or protect.
Follow the steps below to install Wazuh manually starting with the Wazuh indexer:
Prior to installing each component, create any Compute Instances you wish to serve as individual nodes and save their IP addresses. See Wazuh’s documentation for hardware recommendations for nodes running the Wazuh indexer and nodes running the Wazuh server.
Wazuh recommends the following distributions for installation: Red Hat Enterprise Linux 7, 8, 9; CentOS 7, 8; Amazon Linux 2; Ubuntu 16.04, 18.04, 20.04, 22.04
Once all of your nodes have been created, proceed by downloading the Wazuh installation assistant and the configuration file to a machine running one of the above operating systems. Note that installation requires root user access:
curl -sO https://packages.wazuh.com/4.7/wazuh-install.sh curl -sO https://packages.wazuh.com/4.7/config.ymlUsing a text editor, edit the
config.ymlfile and replace the placeholders with names of your nodes along with their corresponding IP addresses. This must be done for each Wazuh indexer, Wazuh server, and Wazuh dashboard nodes:1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28nodes: # Wazuh indexer nodes indexer: - name: node-1 ip: "<indexer-node-ip>" #- name: node-2 # ip: "<indexer-node-ip>" #- name: node-3 # ip: "<indexer-node-ip>" # Wazuh server nodes # If there is more than one Wazuh server # node, each one must have a node_type server: - name: wazuh-1 ip: "<wazuh-manager-ip>" # node_type: master #- name: wazuh-2 # ip: "<wazuh-manager-ip>" # node_type: worker #- name: wazuh-3 # ip: "<wazuh-manager-ip>" # node_type: worker # Wazuh dashboard nodes dashboard: - name: dashboard ip: "<dashboard-node-ip>"
Tip: Node Names When specifying the names of your nodes, it can be helpful to use the same names as your corresponding Compute Instances.After editing your config file, execute the assistant with the
--generate-config-filesoption to generate the Wazuh cluster key, certificates, and passwords necessary for installation. When running the installation script, you may need to use the-ioption to ignore hardware system checks if you are using a distribution not recommended by Wazuh:bash wazuh-install.sh --generate-config-filesYou can find the generated files in the
./wazuh-install-files.tararchive.Copy your
wazuh-install-files.tararchive to all nodes in your deployment, including the Wazuh server, the Wazuh indexer, and the Wazuh dashboard nodes using thescputility. Replace IP_ADDRESS with the IP of the node to which you are copying your.tarfile:scp wazuh-install-files.tar root@IP_ADDRESS:rootIf you haven’t done so already, proceed to download the installation assistant on the node or nodes you designated for the Wazuh indexer:
curl -sO https://packages.wazuh.com/4.7/wazuh-install.shExecute the installation assistant with the
--wazuh-indexerflag on each node. When specifying a name for the node (i.e. node-1), make sure it matches the name you used in yourconfig.ymlfile in step 3:bash wazuh-install.sh --wazuh-indexer node-1On one of the nodes, rerun the installation script, this time adding the
--start-clusterflag. This initiates the cluster:bash wazuh-install.sh --start-cluster
Repeat steps 6 and 7 for the Wazuh server and Wazuh dashboard nodes, replacing the --wazuh-indexer flag with the --wazuh-server and --wazuh-dashboard flags and their respective node names. Remember that the Wazuh dashboard only needs to be installed on a single node.
To access the Wazuh interface in your browser, navigate to https://WAZUH_DASHBOARD_IP, replacing WAZUH_DASHBOARD_IP with the IP of the node where you installed the Wazuh dashboard. Use the login credentials that were generated as output during the dashboard installation.
Once complete, install the Wazuh agents on the endpoints you wish to monitor and protect. If you have a substantial number of endpoints, consider utilizing an automation tool such as Puppet, Chef, SCCM, or Ansible for agent deployment.
Use Case Configuration
There are many different Wazuh use cases that require specific configurations, including blocking known malicious actors, detecting brute-force attacks, and more. See Wazuh’s documentation on use cases, endpoint security options, and their respective configurations:
More Information
You may wish to consult the following resources for additional information on this topic. While these are provided in the hope that they will be useful, please note that we cannot vouch for the accuracy or timeliness of externally hosted materials.
This page was originally published on