In this week’s digest, we will discuss:
- a Kibana security release;
- a vulnerability in Traefik managing TLS connections; and
- a weak randomness in Webcrypto Keygen on NodeJS
Kibana Security Release
Type Confusion: The program allocates or initializes a resource such as a pointer, object, or variable using one type, but it later accesses that resource using a type that is incompatible with the original type. – MITRE definition
CVSSv3.1: NIST – 8.8 (High) | CVE ID: CVE-2022-1364
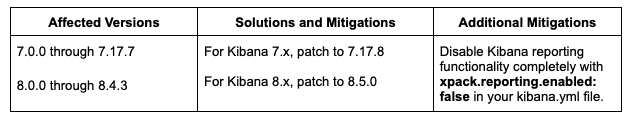
7.17.8, 8.5.0 Security Update: A type confusion vulnerability was discovered in the headless Chromium browser that Kibana relies on for its reporting capabilities. This issue affects only on-premises Kibana instances on host operating systems where the Chromium sandbox is disabled (only CentOS, Debian). This issue does not affect Elastic Cloud, as the Chromium sandbox is enabled by default and cannot be disabled. This issue also does not affect Elastic Cloud Enterprise.
Vulnerability in Traefik Managing TLS Connections
CVSSv3.1:
- NIST – 6.6 (Medium)
- CNA (Github) – 8.1 (High)
CVE ID: CVE-2022-46153
Traefik is a modern HTTP reverse proxy and load balancer. It integrates with your existing infrastructure components (Docker, Swarm mode, Kubernetes, Marathon, Consul, Etcd, Rancher, Amazon ECS) and configures itself automatically and dynamically.
In affected versions, there is a potential vulnerability in Traefik managing TLS connections. A router configured with a not well-formatted TLSOption is exposed with an empty TLSOption. For instance, a route secured using an mTLS connection set with a wrong CA file is exposed without verifying the client certificates. Users are advised to upgrade to version 2.9.6.
Patch: https://github.com/traefik/traefik/releases/tag/v2.9.6
Users unable to upgrade should check their logs to detect the following error messages and fix the TLS options directly:
Empty CA:
{"level":"error","msg":"invalid clientAuthType: RequireAndVerifyClientCert, CAFiles is required","routerName":"Router0@file"}Bad CA content (or bad path):
{"level":"error","msg":"invalid certificate(s) content","routerName":"Router0@file"}Unknown Client Auth Type:
{"level":"error","msg":"unknown client auth type \"FooClientAuthType\"","routerName":"Router0@file"}Invalid cipherSuites:
{"level":"error","msg":"invalid CipherSuite: foobar","routerName":"Router0@file"}Invalid curvePreferences:
{"level":"error","msg":"invalid CurveID in curvePreferences: foobar","routerName":"Router0@file"}Weak Randomness in Webcrypto Keygen on NodeJS
CWE-338: Use of Cryptographically Weak Pseudo-Random Number Generator (PRNG). The product uses a Pseudo-Random Number Generator (PRNG) in a security context, but the PRNG’s algorithm is not cryptographically strong.
CVSSv3.1: NIST – 9.1 (Critical) | CVE ID: CVE-2022-35255
A vulnerability introduced in NodeJS v15.0.0 was discovered by a contributor on HackerOne in which https://github.com/nodejs/node/pull/35093 introduced a call to EntropySource() in SecretKeyGenTraits::DoKeyGen() in src/crypto/crypto_keygen.cc. There are two problems with this:
- Node.js made calls to EntropySource() in SecretKeyGenTraits::DoKeyGen(). However, it does not check the return value and assumes the EntropySource() always succeeds, but it can and sometimes will fail.
- The random data returned byEntropySource() may not be cryptographically strong and therefore not suitable as keying material.
Overall, this flaw allows a remote attacker to decrypt sensitive information.






Comments